I recently had to create an FTP Drop Site for a client. They had photographers that worked remote from home because the main office was either too far or they just did not have any time to stop by and transfer their digital images to the server.
So I created this for them 🙂
This article walks you through creating an FTP site that users can anonymously upload files to, but can’t list or retrieve any files that have been uploaded.
FTP is one of the oldest Internet protocols and still one of the most useful. In olden days, businesses would transfer information by couriers on horseback carrying leather pouches filled with documents. Now most business documents are electronic and are sent over the Internet instead, and while email is often a good way of doing this, some electronic documents are unsuitable for email such as documents too large to serve as attachments or documents that must be submitted anonymously such as surveys. As a result, many businesses still find need for running FTP servers for uploading and downloading large files.
One interesting scenario is when you want customers, clients or business partners to be able to upload files anonymously to your server but not be able to see or download files that others may have uploaded. Such a scenario is often called a “drop box” because it operates like those physical boxes with slots on top that customers can use to fill out satisfaction surveys and drop them in as they leave your store. It’s fairly straightforward to set up such an environment using the FTP service component of Internet Information Services (IIS), and that’s what this article is about.
Preparing the Drop Box
My scenario will be using IIS 6 on a standalone Windows Server 2003 as the FTP server and standalone Windows XP as the client for testing purposes.
We’ll begin by setting up the FTP server. After installing IIS together with the optional FTP service component, I created a new FTP root folder called FTProot on E: drive, a second NTFS drive on the server. The reason for moving FTP content from the default location of C:\Inetpub\Ftproot to E:\Ftproot is security—data should generally be isolated on a different drive than where your operating system is found. This measure also makes it easier to recover from a disaster when you have to reinstall your operating system as that way your data won’t get overwritten during the restore process should you have to reformat your boot volume.
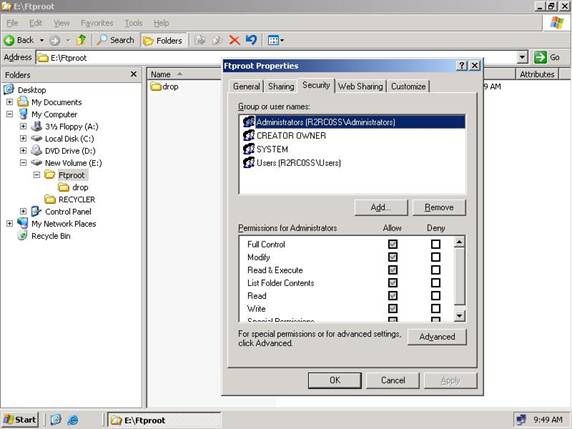
Within the E:\Ftproot folder I next create a folder named drop which I will use as my FTP drop box. The default permissions for my new Ftproot folder in Windows Server 2003 are shown in Figure 1.
Figure 1: Default permissions
Let’s change the permissions on the Ftproot folder to make them more suitable for our purpose. Click the Advanced button to open the Advanced Security Settings dialog box. Then clear the checkbox labeled “Allow inheritable permissions from the parent to propagate to this object…” and when a new dialog box asking you whether you want to copy or remove the existing inherited permissions on the folder, select Copy. The result is that the existing permissions on the Ftproot folder are the same as in Figure 1 but they are now explicit permissions rather than inherited.
Now click OK to close the Advanced Security Settings box and return to the Properties for the Ftproot folder. Remove the ACEs for the following three groups: CREATOR OWNER, SYSTEM, and Users. At this point the only ACE on the Ftproot folder is Administrators have Full Control.
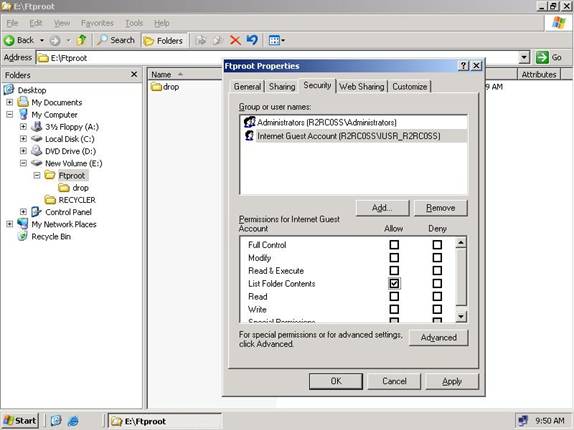
Now click Add and add an ACE for the IIS anonymous user account, which by default is named IUSR_servername where servername is the name of your Windows Server 2003 machine. Then configure the ACE for IUSR_servername so that the account has only List Folder Contents permission allowed as shown in Figure 2.
Figure 2: Configuring the ACE for IUSR_servername
What we have at this point is an Ftproot folder that allows Administrators full access but anonymous users only the ability to list the folder’s contents. These permissions by default are also inherited by the drop subfolder beneath Ftproot, and those permissions need some modification too so now open the Properties sheet for the drop folder, click Advanced, clear the “Allow inheritable permissions…” checkbox, click Copy, and click OK so we can manually modify permissions on the drop folder.
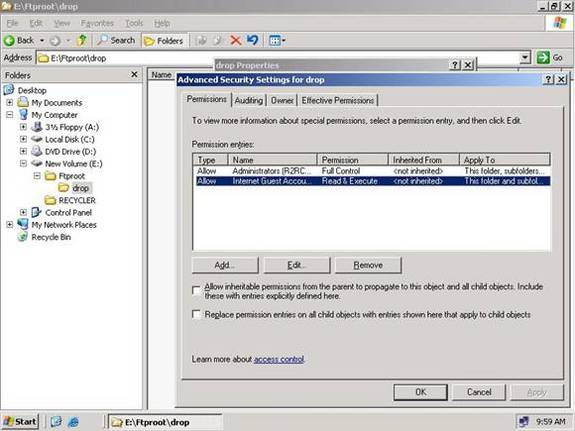
Click the Advanced button again to open the Advanced Security Settings for the drop folder, which should now look like Figure 3:
Figure 3: Advanced Security Settings for the drop folder
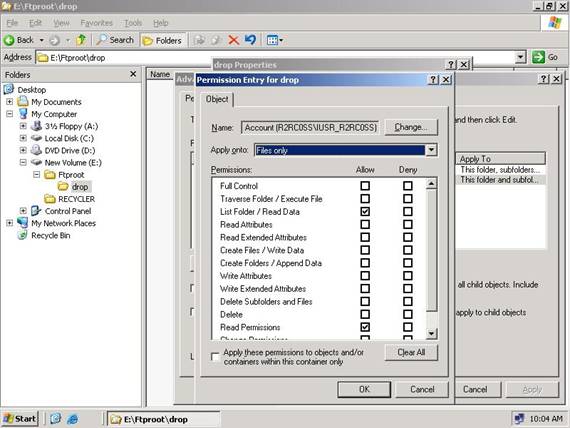
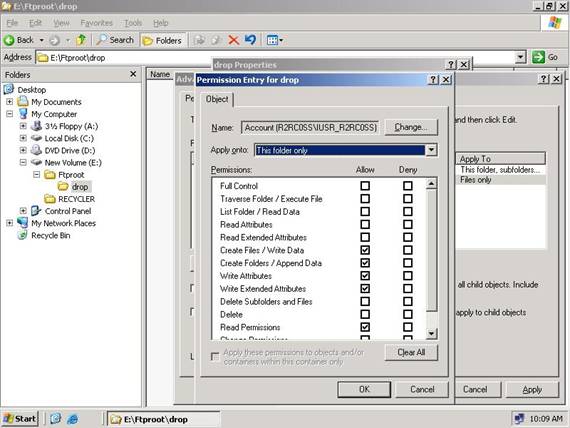
Note that although the standard permissions (ACE on the Properties page) for IUSR_servername was List Folder Contents, here these show up as Read & Execute. We need to tighten the permissions for IUSR_servername even further, so select this identity as shown in Figure 3 and click the Edit button to display the special NTFS permissions for IUSR_servernname. When the Permissions Entry dialog box appears, remove checkmarks beside everything except List Folder/Read Data and Read Permissions, and change the Apply Onto dropdown listbox to Files Only as shown in Figure 4:
Figure 4: Changing the Apply Onto dropdown listbox to Files Only
Click OK to close the Permissions Entry box and modify the special permissions for IUSR_servername. Now we need to create another ACE for IUSR_servername, but this time it will apply to the drop folder itself and not to files within that folder as the ACE in Figure 4 did previously. To create this new ACE, click the Add button, specify IUSR_servername as the account you want to apply permissions to, and configure the permissions as shown in Figure 5:
Figure 5: Creating the new ACE
Click OK several times to close the permissions dialog boxes and you’re done.
Testing the Drop Box
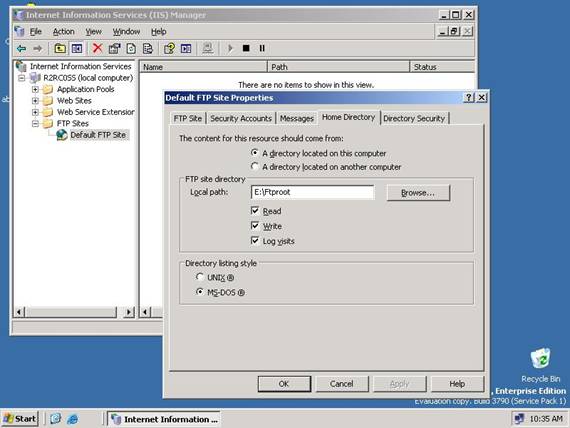
To test our drop box, we’ll first make E:\Ftproot the root folder for the Default FTP Site in IIS. Open IIS Manager, select the FTP Sites node, and under this right-click on Default FTP Site and select Properties. Select the Home Directory tab on this Properties sheet and change the home folder for the site from C:\Inetpub\Ftproot to E:\Ftproot as shown in Figure 6. Don’t forget to also select the Write checkbox to enable uploads to the FTP site.
Figure 6: Changing the home folder for the site
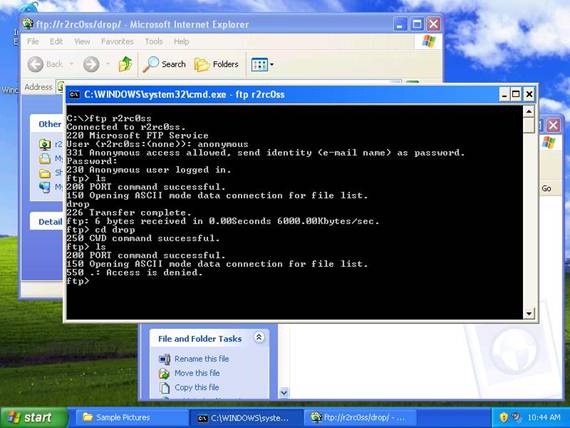
Now let’s test this setup. Using a Windows XP virtual machine running on Virtual PC, I open the My Pictures folder, which has some files I want to upload to the FTP drop box. I then open Internet Explorer and enter the URL for my drop box in the form ftp://servername/drop as shown in Figure 7:
Figure 7: Uploading files to the FTP drop box
Now I drag and drop some picture files from my local My Pictures folder to the drop folder on the remote FTP server. The files should transfer and will be displayed in the Internet Explorer window as residing in the drop folder on the remote machine. If I now refresh the view in Internet Explorer by pressing F5, the displayed files disappear. In other words, once files are uploaded they can’t be seen anymore or by anyone else who accesses the drop folder using an FTP client. To double-check this, I can connect to my drop folder using the Windows command-line ftp.exe client and try to view the contents of the drop folder after uploading some files to it (see Figure 8). The result is that I am denied access when I try to list the contents of the drop folder.
Figure 8: Denied access when tring to list the contents of the drop folder
Using Windows Explorer on my FTP server however, I can easily verify that the files have indeed been successfully uploaded from the XP client machine.
Drop folders like the one I’ve described here can be useful for businesses that need to allow anonymous users to upload large files to your company via FTP. By setting appropriate NTFS permissions on a drop folder on your FTP server, you can allow users to upload files without being able to view or even know about files uploaded by other users.
Got a project that needs expert IT support?
From Linux and Microsoft Server to VMware, networking, and more, our team at CR Tech is here to help.
Get personalized support today and ensure your systems are running at peak performance or make sure that your project turns out to be a successful one!
CONTACT US NOW