What is Password Replication Policy?
Password Replication Policy (PRP) determines which users’ credentials can be cached on a specific RODC.
If PRP allows an RODC to cache a user’s credentials, authentication and service ticket activities of that user can be processed by the RODC.
If a user’s credentials cannot be cached on an RODC, authentication and service ticket activities are referred by the RODC to a writable domain controller.
An RODC’s PRP is determined by two multivalued attributes of the RODC’s computer account. These attributes are commonly known as the Allowed List and the Denied List.
If a user’s account is on the Allowed List, the user’s credentials are cached.
Configuring Domain-Wide Password Replication Policy
To facilitate the management of PRP, Windows Server 2008 R2 creates two domain local security groups in the Users container of Active Directory.
The first group, Allowed RODC Password Replication Group, is added to the Allowed List of each new RODC. By default, the group has no members. Therefore, by default, a new RODC will not cache any user’s credentials.
The second group is named Denied RODC Password Replication Group. It is added to the Denied List of each new RODC.
Configuring RODC-Specific Password Replication Policy
The two groups described in the previous section provide a method to manage PRP on all RODCs. However, to best support a branch office scenario, you must allow the RODC in each branch office to cache credentials of users and computers in that specific location. Therefore, you must configure the Allowed List and the Denied List of each RODC.
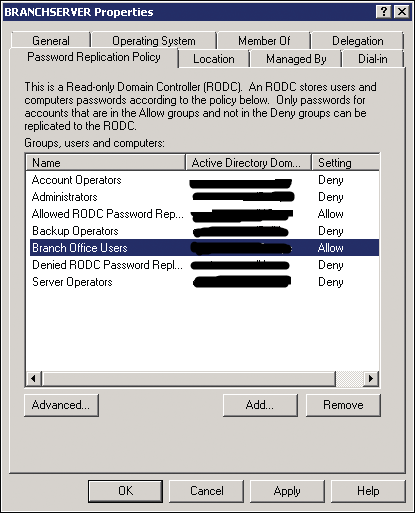
To configure an RODC’s PRP, open the properties of the RODC’s computer account in the Domain Controllers OU. On the Password Replication Policy tab, shown in Figure, you can view the current PRP settings and add or remove users or groups from the PRP.
Administering RODC Credentials Caching
When you click the Advanced button on the Password Replication Policy tab, an Advanced Password Replication Policy dialog box appears.
In the drop-down list at the top of the Policy Usage tab, you can select one of two reports for the RODC:
Accounts Whose Passwords Are Stored On This Read-Only Domain Controller
Displays the list of user and computer credentials that are currently cached on the RODC. Use this list to determine whether credentials are being cached that you do not want cached on the RODC. Then modify the PRP accordingly.
Accounts That Have Been Authenticated To This Read-Only Domain Controller
Displays the list of user and computer credentials that have been referred to a writable domain controller for authentication. Use this list to identify users or computers that are attempting to authenticate with the RODC. If any of these accounts are not being cached, consider adding them to the PRP.
Note: It is not possible for replication to take place between two RODC’s. The changes that are written on a RODC have to come from a writeable DC.
Now let us look at some Active Directory Powershell cmdlets that will help us analyze the same using Powershell.
Add-ADDomainControllerPasswordReplicationPolicy: adds users, computers, and groups to the Allowed List or the Denied List of the RODC Password Replication Policy (PRP).
Get-ADDomainControllerPasswordReplicationPolicy: displays the members of the Allowed List or the Denied List of the RODC PRP.
Remove-ADDomainControllerPasswordReplicationPolicy: removes users, computers, and groups from the Allowed List or the Denied List of the RODC PRP.
Get-ADDomainControllerPasswordReplicationPolicyUsage: displays the resultant password policy of the specified ADAccount on the specified RODC.
Get-ADAccountResultantPasswordReplicationPolicy: displays the resultant password replication policy for an Active Directory account.
I hope this was informative and thank you for reading!
Got a project that needs expert IT support?
From Linux and Microsoft Server to VMware, networking, and more, our team at CR Tech is here to help.
Get personalized support today and ensure your systems are running at peak performance or make sure that your project turns out to be a successful one!
CONTACT US NOW